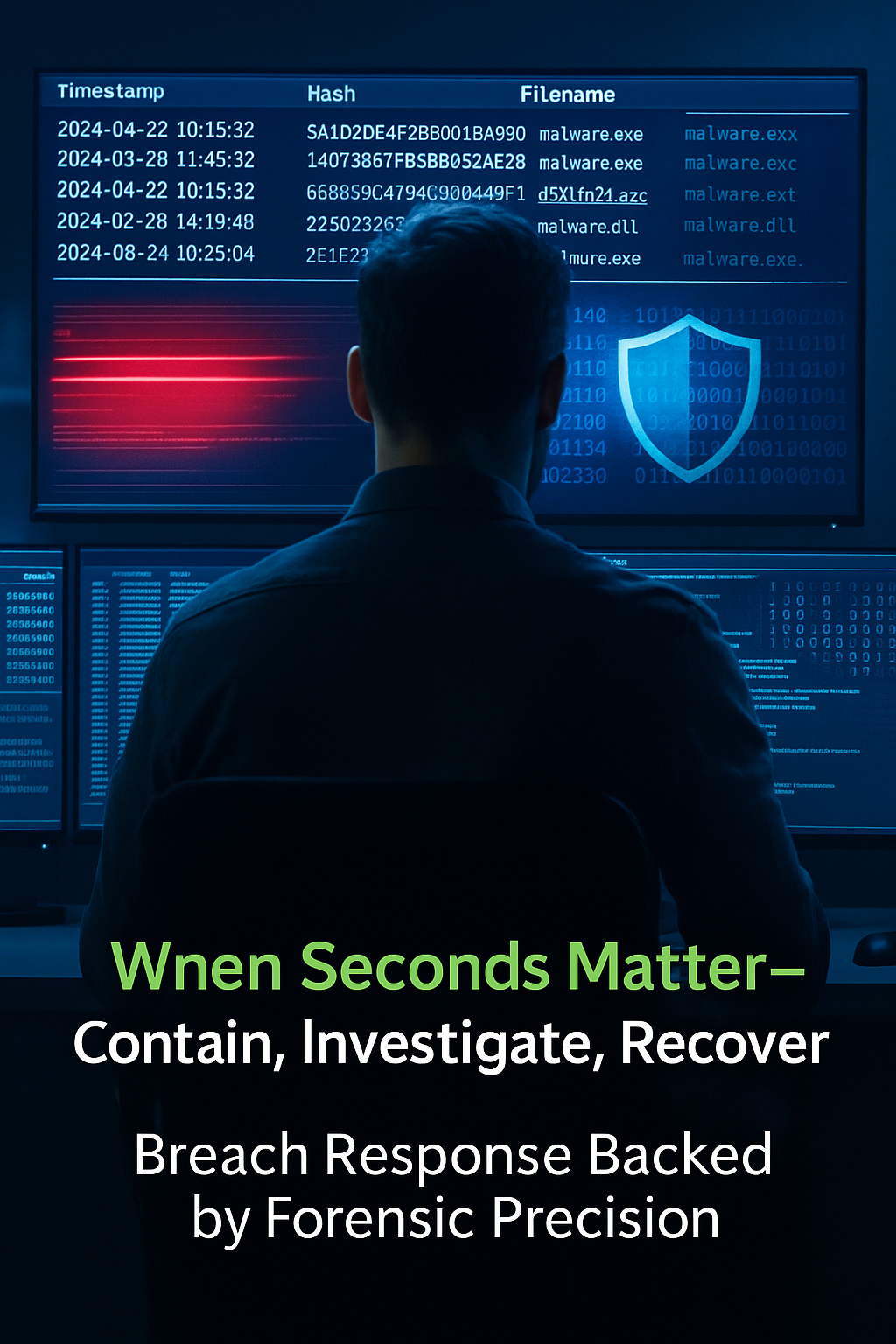
Digital Forensics & Incident Response (DFIR): Rapid Containment. Deep Investigation. Full Recovery.
When a cyber incident strikes, time is everything. From ransomware outbreaks to insider threats and data leaks, Nanosoft’s Digital Forensics & Incident Response (DFIR) team acts fast to contain the threat, investigate the impact, and help you recover with confidence.
Our DFIR experts use advanced forensic tools and threat intelligence to uncover how attackers got in, what they accessed, and how to prevent it from happening again. We assist across the full response lifecycle, from triage and containment to reporting and legal support.
Whether you're experiencing a live breach or preparing your response playbooks in advance, Nanosoft ensures you're never caught off guard.
-
Incident Triage & Threat Containment
Immediate steps to isolate affected systems, stop attacker activity, and preserve evidence.
-
Digital Forensic Investigation
Deep-dive analysis of endpoint, network, and cloud artifacts to determine the attack vector and root cause.
-
Malware & Ransomware Analysis
Reverse engineering of malware and ransomware to understand functionality and potential persistence.
-
Regulatory Breach Reporting Support
Assist with GDPR, ICO, HIPAA, and other breach notifications, with legal-friendly incident summaries.
-
Post-Incident Remediation & Hardening
Close vulnerabilities, review logs, rebuild trust, and secure your infrastructure against repeat attacks.
-
Threat Intelligence Enrichment
Correlate indicators of compromise (IOCs) with global threat feeds for proactive defenses.